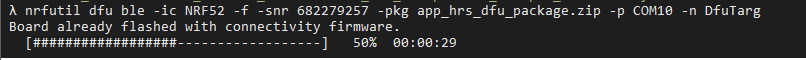
This blog is to introduce how to use the nRFUtil for Over The Air upgrade (OTA) in between host and device. I would focus on the BLE OTA only. It uses the nRF52 DK to connect to PC / Linux / MacOS. And then the nRFUtil tool would be the OTA host application.
nRFUtil
The nRF Util application is a Python package and command-line utility that supports Device Firmware Update (DFU) and cryptographic functionality.
You can get the tool at
https://github.com/NordicSemiconductor/pc-nrfutil/
The nRF Util application and its library has the following features:
- DFU package generation
- Cryptographic key generation, management, and storage
- Bootloader settings generation
- DFU procedure on the following protocols:
- Bluetooth® Low Energy
- Serial over UART
- Serial over USB
- Thread unicast
- Thread multicast
- Zigbee
- ANT™
The user manual of the nRFUtil can be downloaded at
http://infocenter.nordicsemi.com/pdf/nrfutil_v1.7.pdf
Step A: Generating and displaying keys
The keys command can be used to generate and display cryptographic keys.
Cryptographic keys are required to sign and validate a DFU package. See the Cryptography library in the SDK for more information about signing and cryptographic keys.
- Run nrfutil keys generate to generate a private (signing) key and store it in a file in PEM format.
- Run nrfutil keys display to display a private (signing) or public (verification) key from a PEMfile.
You can see available options by entering the following command:
nrfutil keys display --helpFor example, enter the following command to generate a private key and store it in a file named
private.pem:
nrfutil keys generate private.pemEnter the following command to display a public key in code format from this key file:
nrfutil keys display --key pk --format code private.pem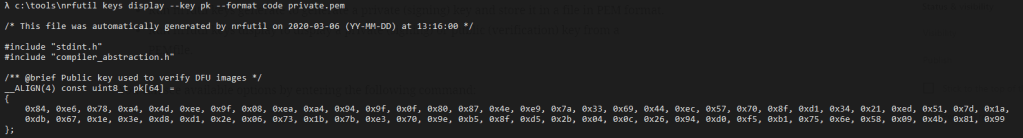
Generate your public key based on your private key.
nrfutil keys display --key pk --format code private.pem --out_file public_key.c
Step B. Generate DFU .zip packet
A DFU .zip packet is required for the DFU master to send new image(s) to the DFU target. The .zip file contains the image hex file(s) we want to update and the init packet, including the signature of the packet. In the main part of this guide, we only do application image update.
B1. Prepare the application hex file. Build your application and find the .hex file inside _build folder. Usually it’s named nrf52840_xxaa.hex if you compile a SDK’s example. Flash the application hex and verify it works normally without the bootloader (flash softdevice if needed).
B2. Generate the .zip file. Copy the private.key generated in step A1 to the same folder with your .hex application file.
Get the softdevice version ID
The most up to date list of softdevice ID can be found in the source code or nRFUtil.
https://github.com/NordicSemiconductor/pc-nrfutil/blob/master/nordicsemi/__main__.py#L501
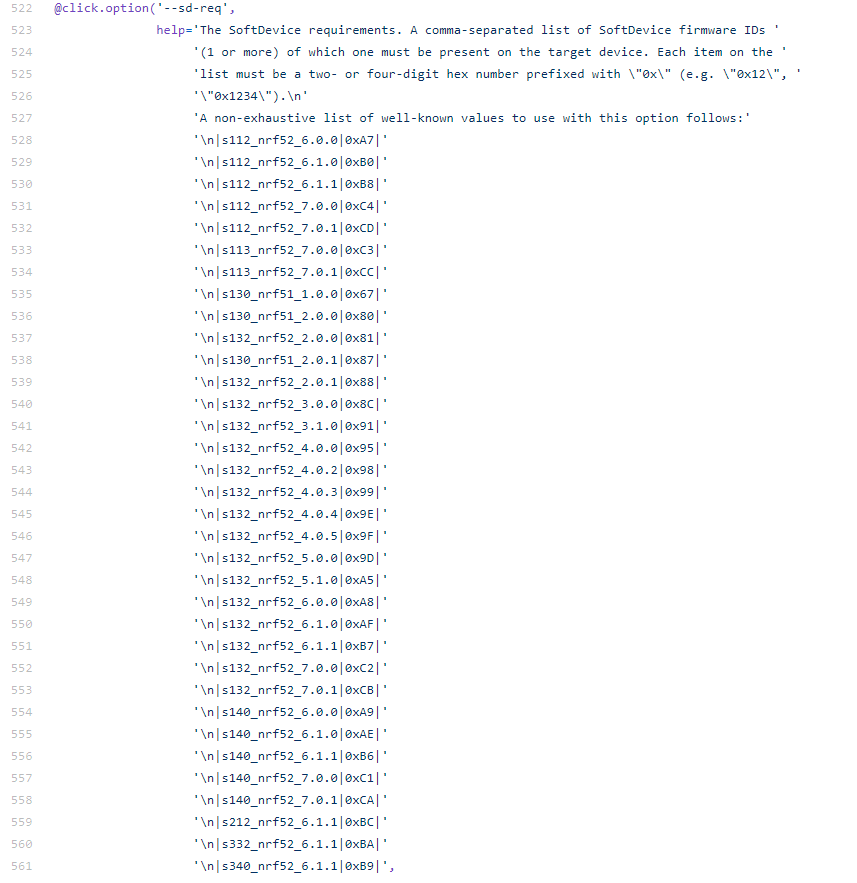
In this example, I am using the Nordic nRF5 SDK (version 16.0) and the softdevice S140v7.0.1 (0xCA)
Also, I built two ble applications.
- ble_app_hrs
- ble_app_uart
nrfutil pkg generate --hw-version 52 --application-version 1 --application ..\ble_app_hrs_pca10056_s140.hex --sd-req 0xca --key-file private.pem app_hrs_dfu_package.zip
Zip created at app_hrs_dfu_package.zipnrfutil pkg generate --hw-version 52 --application-version 1 --application ..\ble_app_uart_pca10056_s140.hex --sd-req 0xca --key-file private.pem app_uart_dfu_package.zip
Zip created at app_uart_dfu_package.zipStep C. Performing DFU
Now you have your DFU .zip file and the bootloader ready, it’s time to actually do DFU.
Check on the COM port
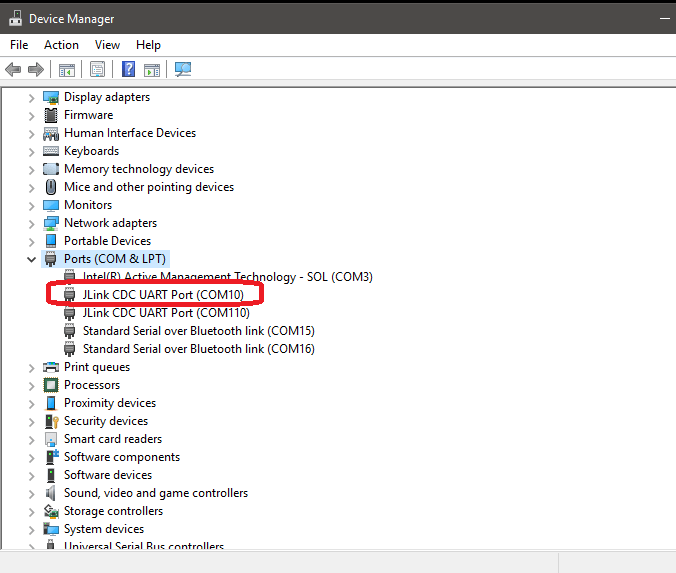

Manually program the connectivity hex firmware on the DK board
In the meantime, it is possible to flash it manually, using nRF Connect for Desktop, and then use nrfutil from the command line, or in a script. If you install e.g. pc_ble_driver_py, the hex file for the dongle that is used in nrfutil will be present in Python\Lib\site-packages\pc_ble_driver_py\hex\sd_api_v5
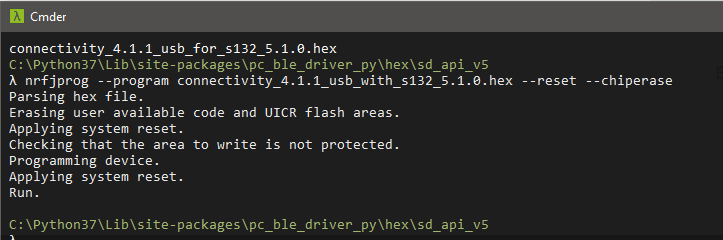
Use the nrfutil to program the connectivity firmware
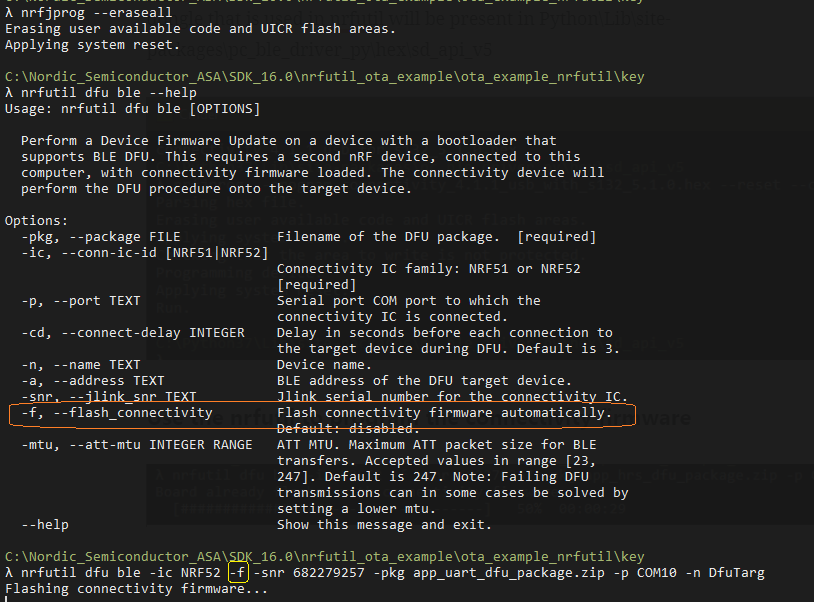
Use the command line to upgrade the firmware on device
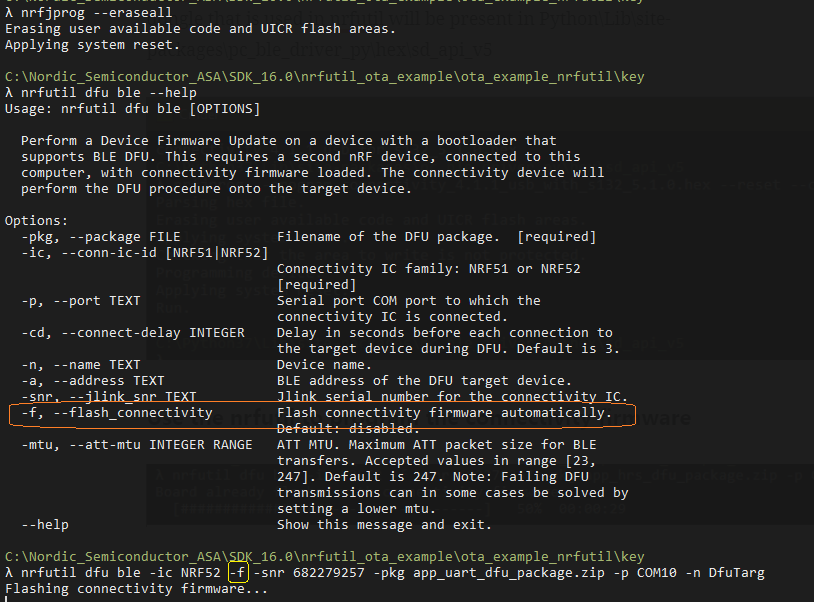
Use the nrfUtil command to upgrade the firmware of device
All the materials can be found at https://github.com/jimmywong2003/nrf52840-dfu-through-nrfutil-example.
If you have any question, welcome to leave the message to me here.
Thanks for your interests on my blog. Since 2019, I have created this blog and shared the idea how to do some funny stuffs. I am very pleasure that I get quite a lot of positive feedback. I really hope that this blog helps your own embedded solution development. May I get support from you to keep it in order to maintain the wordpress host service? Your appreciation would be very helpful.
https://jimmywongiot.com/2021/05/26/asking-for-support/

hello
I get the error : No such option: –hw-version, when I try to build the package
LikeLike
You can check on the nRFutil github to see the option.
LikeLike